South Florida’s February 2016 meeting will be on Thursday, February 18th, 2016 at Nova Southeastern University. The meeting will take place in the Carl DeSantis Building from 6PM to 9:30PM, followed by their usual networking hour.
Presentation One
Title:
Artificial Intelligence – Real Threat Prevention
Speaker:
Clayton Fields
Bio:
Clayton Fields is Regional Director for Cylance in the Southeast. He has spent the last 10 years helping clients navigate the landscape of solutions for the datacenter and endpoint. Before joining Cylance, Clayton worked with SecureWorks to provide clients with vulnerability management, intrusion detection, incident response services, and cyberthreat hunting. SecureWorks was acquired by Dell. At Cylance, Clayton works with clients to understand the weaknesses of human controls and where artificial intelligence can enhance threat mitigation.
Presentation Two
Title:
NIST-based Information Risk Management Essentials and Maturity
Speaker:
Bob Chaput
Abstract:
Even with the dramatic increase in the number and severity of data breaches in all industries, including huge increases in healthcare organizations, too many organizations are still disengaged from holistic, mature information risk management. Many organizations are stuck in a tactical-technical-spot-welding loop when they should be moving to adoption of an industry-standard framework and a more strategic-business-architectural approach. Organizations must begin to mature their information risk management programs, and the use of a risk management maturity model can assist in that improvement, allowing an organization to have its methods and processes assessed according to management best practices, against a clear set of external benchmarks. In this session, we will cover the essentials of establishing, operationalizing and maturing an information risk management program using the NIST Security Process as a starting point.
KEY LEARNING OBJECTIVES FOR THE PRESENTATION:
1. Speak the “language of risk”
2. Describe the 4-Step NIST Information Risk Management Process
3. Access NIST and other resources to assist organizations in Information Risk Management
4. Explain the essential steps of establishing, operationalizing and maturing an information risk management program
Bio:
Over the past 35 years, Bob has worked as an educator, an executive and an entrepreneur. He assists businesses in developing highly effective privacy, security, compliance and information risk strategies that are tightly linked with their business strategies and goals. Bob is no stranger to managing and protecting large amounts of data – his experience includes managing some of the world’s largest and most sensitive financial, HR, benefits and healthcare databases, requiring the most stringent levels of controls. Bob’s experience as an EVP & CIO and general manager in leading publicly-traded global organizations at GE, Johnson & Johnson and Healthways for 30+ years equips him to help leaders make informed decisions about information privacy and security investments. His business career spans many years of increasingly greater responsibility for all aspects of regulatory compliance and information security, with 25+ of those years covering the highly regulated healthcare industry. Mr. Chaput earned his undergraduate and graduate degrees in mathematics and two advanced post-graduate certificates from the Vanderbilt University School of Engineering. He holds numerous certifications in privacy, security, compliance and risk management.
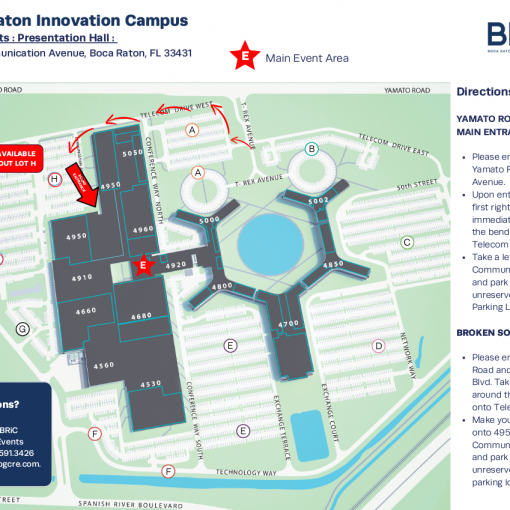
Venue and Map
Location:
Nova Southeastern University – Carl DeSantis Building
3301 College Avenue
Fort Lauderdale, Florida 33314
Phone: 800-541-6682
Map:
Sponsors:
Cylance
![]()
Clearwater Compliance